
AWS WAF Magento: Configuration and Best Practices
[Updated: March 20, 2026]
A single unblocked SQL injection can expose your entire customer database. A bot flood during a flash sale can crash your checkout. AWS WAF stops both before they reach your Magento application.
This guide covers the complete AWS WAF setup for Magento 2.4.8, including Bot Control, AI threat mitigation, managed rules, custom rules, and a full pricing breakdown.
Key Takeaways
- AWS WAF filters malicious traffic at the edge before it reaches your Magento 2.4.8 store, blocking SQL injection, XSS, and bot attacks
- Bot Control detects 16 bot categories including AI scrapers and automated browsers using machine learning
- Intelligent Threat Mitigation adds account takeover prevention, fraud detection, and DDoS protection
- Base cost starts at $6.60/month for a single Web ACL with one rule and 1 million requests
- Integration with CloudFront, Application Load Balancer, and API Gateway requires zero changes to your Magento codebase
What Is AWS WAF?
AWS WAF = A web application firewall by Amazon Web Services that inspects HTTP/HTTPS traffic and blocks malicious requests based on rules you define. It protects at the application layer without touching your server infrastructure.
Perfect for: Magento stores on AWS, ecommerce sites handling payment data, stores targeted by bots or scraping attacks
Not ideal for: Static sites with no user input, stores not hosted on AWS infrastructure
AWS WAF operates between the internet and your Magento application. Every incoming request passes through your Web ACL (Access Control List), a collection of rules that decide whether to allow, block, or count each request.
The firewall inspects IP addresses, HTTP headers, URI strings, query parameters, and request bodies. It catches SQL injection attempts, cross-site scripting (XSS), and malformed requests before your Magento PHP process ever sees them.
AWS WAF runs at the edge. When paired with Amazon CloudFront, rules execute across over 750 Points of Presence worldwide. Malicious traffic gets blocked closest to its origin, reducing load on your Magento servers.
How AWS WAF Protects Magento Stores
Magento stores face specific threats that generic firewalls miss. Admin panel brute force attacks, checkout fraud, API abuse, and inventory scraping are common in ecommerce.
AWS WAF addresses these through three protection layers:
Layer 1: Managed Rules. Pre-built rule sets cover OWASP Top 10 vulnerabilities. SQL injection patterns, XSS payloads, and known bad inputs get blocked without custom configuration.
Layer 2: Custom Rules. You define rules for your Magento store. Rate-limit login attempts to /admin. Block requests from specific countries. Reject oversized POST bodies that signal buffer overflow attacks.
Layer 3: Intelligent Threat Mitigation. Machine learning analyzes traffic patterns, detects coordinated bot activity, prevents account takeovers, and identifies fraudulent account creation.
AWS WAF Integration with AWS Services
Amazon CloudFront
Amazon CloudFront delivers your Magento store content through a global CDN. When AWS WAF attaches to a CloudFront distribution, every request gets inspected at the nearest edge location.
You create a Web ACL and associate it with your CloudFront distribution. The ACL rules then inspect all incoming requests. Based on your conditions, AWS WAF allows, blocks, or counts each request before it reaches your origin server.
This combination is powerful for Amazon CloudFront integration with Magento. It reduces server load by filtering malicious traffic at the edge while accelerating legitimate requests through CloudFront caching.
Application Load Balancer (ALB)
Application Load Balancers distribute incoming traffic across multiple Magento instances and availability zones. Attaching AWS WAF to an ALB lets you inspect traffic at the load balancer level.
A Web ACL associates with one or more ALB listeners. Every client request to the ALB passes through your WAF rules first. Clean traffic reaches your Magento application. Malicious requests never touch your servers.
This integration works well for Magento stores running multiple instances behind a load balancer, where DDoS protection with AWS Shield adds another defense layer.
Amazon API Gateway
Magento stores with headless frontends or mobile apps expose REST and GraphQL APIs. AWS WAF protects these endpoints by attaching a Web ACL to an API Gateway stage.
The firewall inspects every API call against your rules. SQL injection through API parameters, excessive API calls from a single IP, and parameter tampering get caught before reaching Magento.
Bot Control and AI Threat Protection
Bot traffic accounts for a significant portion of web requests. AWS WAF Bot Control identifies and manages bots across 16 categories, from search engine crawlers to malicious scrapers.
Common Bot Control
Common Bot Control detects self-identifying bots using traditional detection techniques. It analyzes static request data, user-agent strings, and IP reputation.
The rule group categorizes bots into 16 types: search engines, social media crawlers, content fetchers, advertising bots, security scanners, monitoring tools, archivers, email clients, HTTP libraries, link checkers, page preview generators, scraping frameworks, SEO tools, webhooks, AI bots, and miscellaneous.
Verified bots (like Googlebot) pass through. Unverified bots claiming to be legitimate get blocked. This protects your Magento store from scraping while keeping search engine indexing intact.
Common Bot Control costs $10/month per Web ACL plus $1 per million requests. The first 10 million requests each month are free.
Targeted Bot Control
Targeted Bot Control adds machine learning to catch sophisticated bots that evade Common detection. It uses browser fingerprinting, behavioral analysis, and token management.
Key capabilities include:
Volumetric Detection. Flags IPs sending 5+ requests per 5 minutes without a valid token. Abnormal session volumes trigger CAPTCHA challenges.
Token Reuse Detection. Catches distributed attacks where a single token appears from multiple IPs, countries, or ASN networks. Three confidence levels (low, medium, high) trigger progressive responses from counting to blocking.
Browser Signal Detection. Identifies automated browsers (Selenium, Puppeteer), browser automation extensions, and browser interrogation anomalies.
ML Coordinated Activity. Machine learning detects coordinated bot activity at low, medium, and high confidence levels. ML models require up to 24 hours to establish baselines from normal traffic patterns.
Targeted Bot Control costs $10/month per Web ACL plus $10 per million requests. The first 1 million requests each month are free.
AI Bot Management
AWS WAF launched an AI Activity Dashboard in February 2026. This feature provides visibility into AI bot traffic hitting your Magento store.
Three categories of AI bots target ecommerce stores:
- AI scrapers collect product data, pricing, and content to train AI models
- AI tools use function calling to surface your store data in AI applications
- AI agents navigate and interact with your store to perform automated tasks
The Bot Control CategoryAI rule blocks all AI bots, both verified and unverified. This is the only category where verified status does not grant access. For stores that want to allow specific AI crawlers, you create exception rules using labels.
Setting Up AWS WAF for Magento
Step 1: Create a Web ACL
Log into the AWS Management Console and navigate to the WAF & Shield service. Select "Create web ACL" and choose your region. For CloudFront distributions, select "Global (CloudFront)."
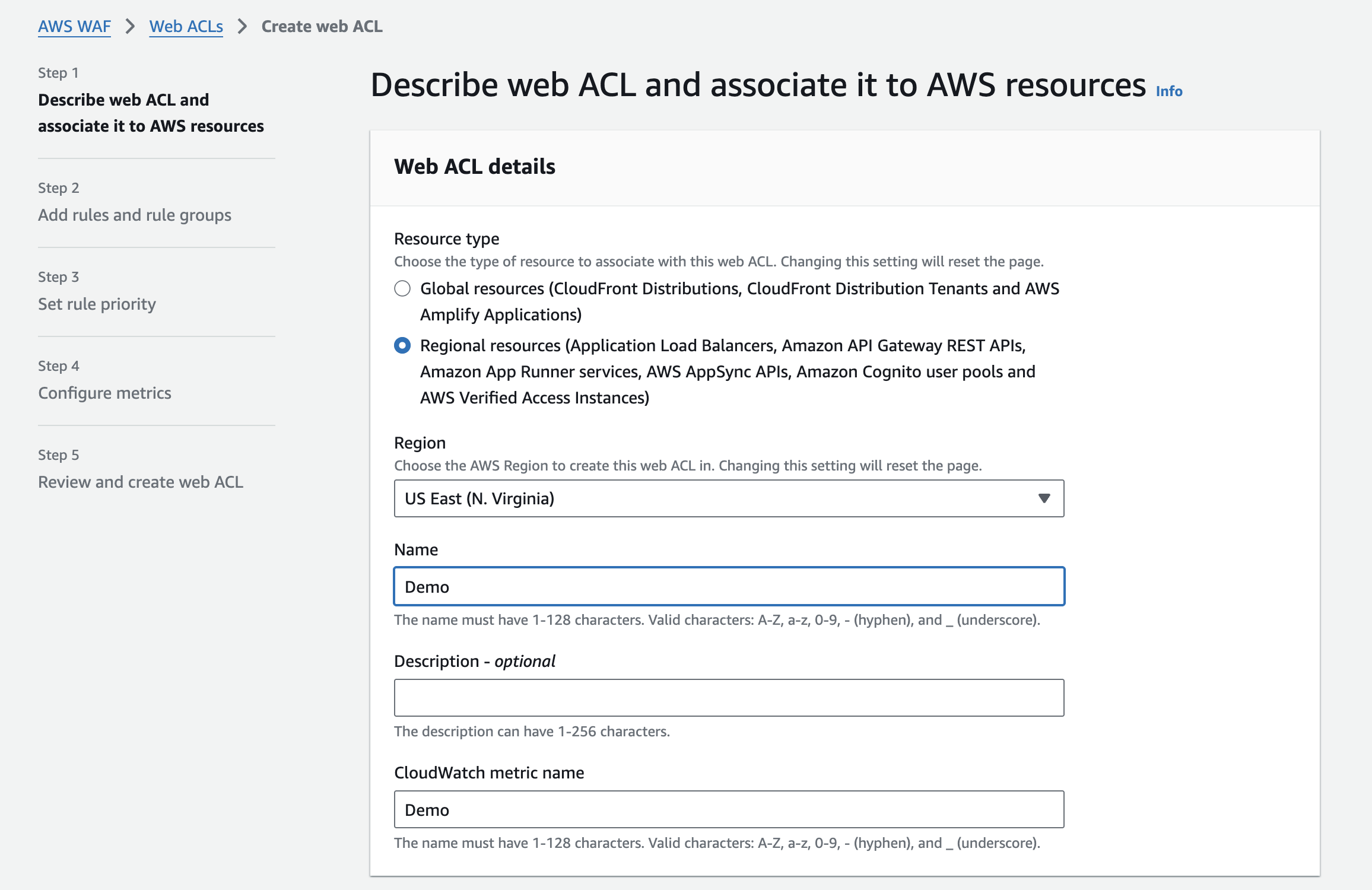
Name your Web ACL and set the default action. "Allow" passes unmatched requests through. "Block" rejects everything not matching an allow rule. For most Magento stores, "Allow" with specific block rules works best.
Step 2: Associate AWS Resources
Attach the Web ACL to your AWS resources. Select your CloudFront distribution, Application Load Balancer, or API Gateway stage. You can protect multiple resources with a single Web ACL.
Step 3: Add Managed Rules
Add AWS Managed Rule Groups first. The essential groups for Magento stores:
- AWSManagedRulesCommonRuleSet covers OWASP Top 10 threats
- AWSManagedRulesSQLiRuleSet blocks SQL injection patterns
- AWSManagedRulesKnownBadInputsRuleSet catches known exploit payloads
- AWSManagedRulesBotControlRuleSet manages bot traffic (optional, additional cost)
Step 4: Create Custom Rules
Add rules specific to your Magento store. Rate-limit the /admin path to prevent brute force attacks. Block countries outside your service area with geo-match conditions. Set size constraints on request bodies to catch buffer overflow attempts.
Step 5: Set Rule Actions and Priority
Configure each rule with an action: allow, block, or count. Start new rules in "Count" mode to monitor their impact before enforcing them. Order rules by priority, placing cheaper standard rules before paid rule groups.
Step 6: Test and Deploy
Use Count mode for 48 to 72 hours before switching to Block. Monitor CloudWatch metrics for false positives. Check that legitimate Magento admin access, API calls, and customer checkout flows work without interruption.
AWS WAF Pricing for Magento Stores
AWS WAF uses pay-as-you-go pricing with no upfront commitments. Costs scale with your traffic and the rule groups you enable.
Base Pricing
| Component | Cost |
|---|---|
| Web ACL | $5.00/month |
| Rule (custom or managed group) | $1.00/month per rule |
| Requests inspected | $0.60 per million |
| CAPTCHA attempts | $0.40 per 1,000 |
| Oversized body inspection | $0.30 per million (each 16KB beyond default) |
Bot Control and Fraud Prevention Add-Ons
| Feature | Monthly Fee | Request Fee | Free Tier |
|---|---|---|---|
| Common Bot Control | $10.00/Web ACL | $1.00/million | First 10M requests |
| Targeted Bot Control | $10.00/Web ACL | $10.00/million | First 1M requests |
| Account Takeover Prevention (ATP) | $10.00/Web ACL | Per-request fee | None |
| Account Creation Fraud Prevention (ACFP) | $10.00/Web ACL | Per-request fee | None |
Cost Examples for Magento Stores
Small store (100K monthly requests, basic protection): Web ACL ($5) + 3 managed rule groups ($3) + requests ($0.06) = about $8/month
Medium store (5M monthly requests, Bot Control): Web ACL ($5) + 5 rules ($5) + requests ($3) + Common Bot Control ($10) = about $23/month
Large store (50M monthly requests, full protection): Web ACL ($5) + 8 rules ($8) + requests ($30) + Targeted Bot Control ($10 + $490) + ATP ($10) = about $553/month
Costs reduce when you use scope-down statements to limit which requests reach paid rule groups. Run standard AWS WAF rules first, then Bot Control, then ATP, then ACFP. This order minimizes the number of requests evaluated by expensive rule groups.
Securing Magento Endpoints
Admin Panel
The /admin path gives access to your entire store backend. Protect it with:
- Rate-based rules limiting login attempts per IP (10 per 5 minutes is a good baseline)
- Geo-match conditions restricting admin access to your team's countries
- IP set rules allowing admin access from specific office or VPN IPs
Checkout and Payment Pages
Checkout pages handle credit card data and are targets for credential stuffing and payment fraud. Apply the PCI DSS compliance requirements through WAF rules that enforce strict input validation, block known attack patterns, and rate-limit checkout attempts.
REST and GraphQL APIs
Magento 2.4.8 exposes REST and GraphQL APIs for headless frontends, mobile apps, and third-party integrations. Protect these with:
- Authentication validation rules
- Rate limiting per API endpoint
- Size constraint rules on request payloads
- Input validation for query parameters
Follow your overall security hardening guide to ensure WAF rules complement your application-level security.
Compliance and Data Security
AWS WAF helps meet regulatory requirements for ecommerce stores handling sensitive customer data.
PCI DSS. Magento stores processing credit cards must meet PCI DSS requirements. AWS WAF provides required controls for securing cardholder data, filtering malicious input, and logging access attempts.
GDPR. European stores must protect personal data. WAF rules can inspect and filter outbound responses to prevent data leakage, block unauthorized access patterns, and maintain audit logs.
AWS WAF logging captures full details of every inspected request. Send logs to Amazon S3, CloudWatch Logs, or Kinesis Data Firehose for analysis. These logs support compliance audits and incident investigations.
Pros and Cons of AWS WAF for Magento
| Pros | Cons |
|---|---|
| Edge-level filtering before traffic hits servers | Only works with AWS infrastructure |
| Pay-as-you-go with no upfront commitment | Targeted Bot Control gets expensive at high traffic |
| ML-based bot detection catches sophisticated threats | ML baselines need 24 hours to establish |
| Managed rules auto-update against new threats | Custom Magento rules require manual maintenance |
| Integrates with CloudFront, ALB, and API Gateway | No protection for non-AWS hosted resources |
FAQ
What is AWS WAF and how does it protect Magento?
AWS WAF is a web application firewall that inspects HTTP/HTTPS traffic before it reaches your Magento store. It blocks SQL injection, XSS, bot attacks, and other threats based on rules you configure in a Web ACL.
How much does AWS WAF cost for a Magento store?
Base cost starts at about $8/month for a small store with basic managed rules. A medium store with Bot Control runs about $23/month. Large stores with full Targeted Bot Control and fraud prevention can reach $500+/month depending on traffic volume.
Can AWS WAF block AI bots from scraping my Magento store?
Yes. The Bot Control CategoryAI rule blocks all AI bots including scrapers, AI tools, and AI agents. This applies to both verified and unverified AI bots. You can create exception rules for specific AI crawlers you want to allow.
Does AWS WAF work with Magento 2.4.8?
AWS WAF operates at the infrastructure level, independent of your Magento version. It attaches to CloudFront, ALB, or API Gateway. No Magento code changes or extensions are required. It works with Magento 2.4.8 running PHP 8.3 or 8.4.
What managed rules should I enable first for Magento?
Start with AWSManagedRulesCommonRuleSet (OWASP Top 10), AWSManagedRulesSQLiRuleSet (SQL injection), and AWSManagedRulesKnownBadInputsRuleSet (known exploits). Add Bot Control after establishing baseline traffic patterns.
How do I prevent false positives from blocking legitimate Magento traffic?
Deploy new rules in Count mode for 48 to 72 hours. Monitor CloudWatch metrics and WAF logs for legitimate requests matching your rules. Create exception rules for known good patterns. Test admin access, checkout flows, and API calls after every rule change.
Can AWS WAF protect my Magento admin panel from brute force attacks?
Yes. Create a rate-based rule targeting your admin URL path. Limit login attempts to 10 per IP per 5-minute window. Combine with geo-match conditions to restrict admin access to specific countries or IP sets for your team.
What is the difference between Common and Targeted Bot Control?
Common Bot Control detects self-identifying bots using static analysis and costs $1 per million requests. Targeted Bot Control adds ML-based detection, browser fingerprinting, and behavioral analysis at $10 per million requests. Targeted catches sophisticated bots that evade Common detection.
Does AWS WAF help with PCI DSS compliance for Magento?
AWS WAF provides security controls required by PCI DSS, including input validation, access logging, and malicious traffic filtering. It does not replace a full PCI audit but strengthens your compliance posture for payment data protection.
Should I use AWS WAF or a third-party WAF for Magento?
AWS WAF integrates native with CloudFront, ALB, and API Gateway. If your Magento store runs on AWS, this integration delivers lower latency and simpler management than third-party alternatives. Stores on non-AWS hosting need a different WAF solution.
Summary
AWS WAF adds a proven security layer to your Magento 2.4.8 store without code changes or performance penalties. Managed rules handle OWASP threats out of the box. Bot Control catches automated scrapers and AI bots with machine learning. Custom rules protect Magento-specific endpoints like admin panels, checkout pages, and APIs.
Pricing starts under $10/month for basic protection and scales with your traffic. The Count mode lets you test every rule before enforcement, eliminating false positive risk.
For stores running on AWS hosting infrastructure, AWS WAF is the natural choice. It runs at the edge through CloudFront, handles millions of requests with sub-millisecond latency, and updates managed rules against new threats without manual intervention.
Pair AWS WAF with managed Magento hosting that includes pre-configured security, auto-scaling, and 24/7 monitoring. Your store gets enterprise-grade protection without the operational overhead.

