
Magento Security Scan Tool: Setup Guide and Best Alternatives
[Updated: March 16, 2026]
A single unpatched vulnerability can expose your entire customer database. The Magento Security Scan Tool catches threats before they become breaches, running over 21,000 security tests at no cost.
This guide covers the complete setup process, explains what the tool can and cannot detect, and reviews the best third-party alternatives for full store protection.
Key Takeaways
- The Magento Security Scan Tool runs 21,000+ security tests and is free for all Adobe Commerce and Magento Open Source users.
- Adobe partners with Sansec, which maintains 50,000+ malware signatures and scans 400,000+ stores each day.
- The built-in tool does not scan file systems or databases. Third-party scanners like Sansec eComscan and MageReport cover this gap.
- Schedule scans at least once per week. Run manual scans after each extension install, version upgrade, or custom code deployment.
- Combine scanning with 2FA, a web application firewall, and regular patch updates for full protection.
What Is the Magento Security Scan Tool?
Magento Security Scan Tool = A free Adobe service that monitors your store for malware, vulnerabilities, and missing patches. Runs 21,000+ tests but cannot scan your file system or database.
Perfect for: Magento store owners, developers managing multiple sites, agencies monitoring client stores.
Not ideal for: Stores that need deep file-level malware detection or real-time threat monitoring.
The Magento Security Scan Tool is available through your Adobe Commerce or Magento Open Source account dashboard. Adobe built it in partnership with Sansec, a Dutch ecommerce security firm that maintains over 50,000 malware signatures and inspects 400,000+ online stores each day.
The tool delivers:
- Malware detection across 21,000+ security tests
- Patch monitoring with alerts for missing security patches
- Scheduled scans on a daily, weekly, or on-demand basis
- Historical reports to track your store's security posture over time
- False positive management to ignore known safe configurations
It supports all current Magento versions: Magento Open Source 2.4.x, Adobe Commerce, and Adobe Commerce on Cloud Infrastructure. The latest stable release as of March 2026 is Magento 2.4.8-p4.
How the Security Scan Tool Works
The scanner runs from Adobe's infrastructure. It requires no software installation on your server. After you verify domain ownership and configure scan settings, the tool connects to your storefront and runs its full test suite.
Each scan checks for:
- Known malware signatures from Sansec's database of 50,000+ threats
- Missing security patches for your Magento version
- Common vulnerability patterns including exposed admin URLs, weak configurations, and outdated components
- Unauthorized modifications to core files accessible through the storefront
Results fall into three categories: successful checks, failed checks (with recommended actions), and unidentified checks (items that need manual review).
What the Tool Does NOT Detect
The built-in scanner operates from outside your server. It cannot inspect your file system, database, or server processes. File-level malware injections, skimmer scripts hidden in database entries, and compromised cron jobs all require server-side scanning tools. This is why third-party scanners remain essential for complete protection.
How to Set Up the Magento Security Scan Tool
Step 1: Activate Security Scan in Your Adobe Account
- Log in to your Adobe Commerce account.
- Click Security Scan in the left panel.
- Click Go to Security Scan.
- Review and accept the Terms and Conditions.

Step 2: Add Your Site and Verify Domain Ownership
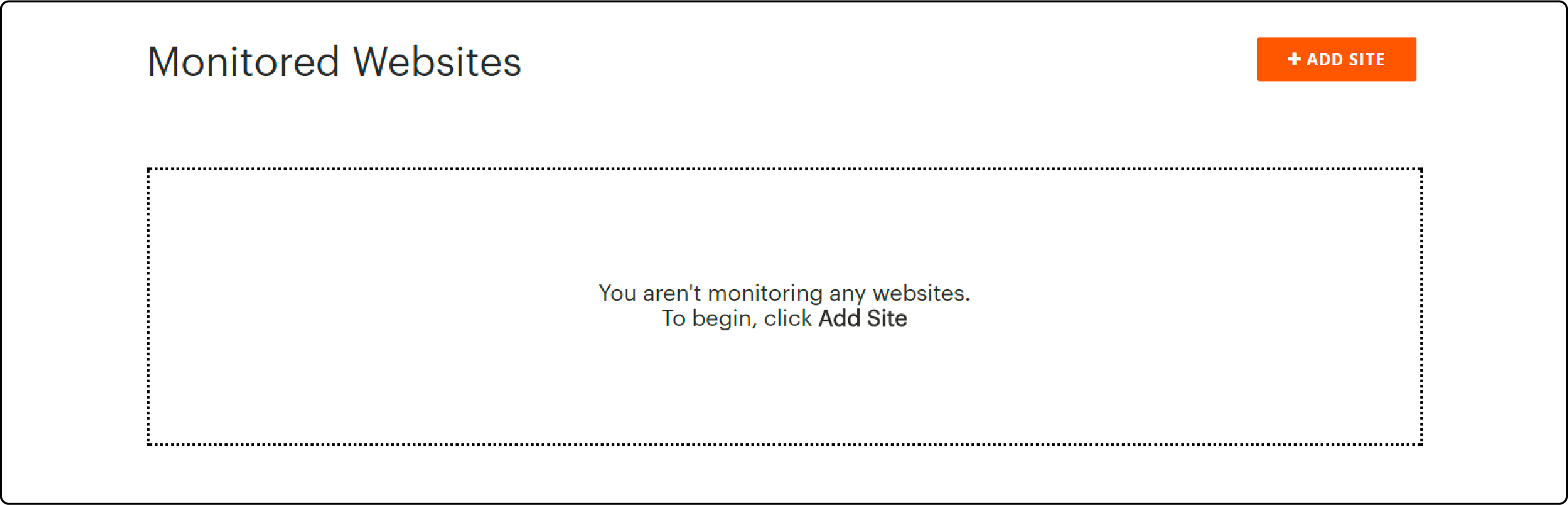
On the Monitored Websites page, click +Add Site. Enter your Site URL and Site Name.
Adobe requires domain verification before scanning starts. The process depends on your storefront type:
Standard Commerce Storefront:
- Click Generate Confirmation Code and copy the META tag.
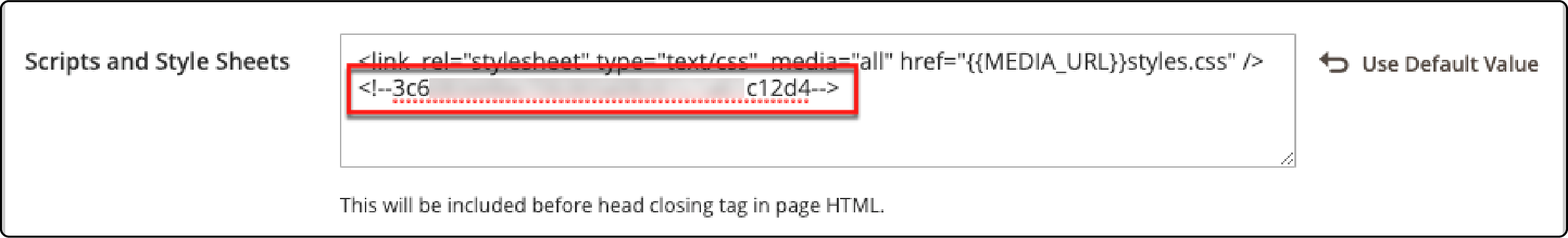
- In your Magento Admin, go to Content > Design > Configuration.
- Find your site and click Edit.
- Open the HTML Head section and paste the code into Scripts and Style Sheets.
- Save the configuration.
PWA Storefront:
- Generate the META Tag confirmation code.
- Add it to
packages/venia-concept/template.htmlin the<head>section. - Run
yarn install && yarn build. - Deploy to your Cloud project via Git.
AEM (Adobe Experience Manager) Storefront:
- Choose HTML Content or META Tag format.
- Add the code to the
head.htmlfile. Do not use CMS editing tools for this step. - Deploy via Git CLI.
Return to the Security Scan page and click Verify Confirmation Code. If you manage multiple domains, including staging environments, configure a separate scan for each domain.
Step 3: Configure Automatic Scanning
- Select Scan Weekly (recommended) or Scan Daily.
- For weekly scans, set your preferred day, time, and timezone. The default runs Saturday at midnight UTC.
- For daily scans, set the time and timezone.
- Enter the email address for scan completion notifications.
- Click Submit.

Step 4: Run a Scan and Review Results
Run an immediate on-demand scan or wait for the next scheduled scan. Results are organized into three tables:
- Successful Scans confirm your store passes specific security checks.
- Failed Scans flag vulnerabilities with recommended actions.
- Unidentified Scans indicate checks that could not complete, often due to access restrictions.
Focus on failed checks first. Each includes a description and a recommended fix. For complex vulnerabilities, engage your development team or add a Magento 2 security extension for extra protection.
Step 5: Manage False Positives
Not every failed check represents a real threat. The tool includes an Ignore feature for known false positives:
- Patches applied through alternative methods
- Configurations correct for your specific environment
- Security measures implemented outside the tool's detection scope
Mark these as ignored to exclude them from your risk score. You can restore ignored items to active monitoring at any time.
Third-Party Magento Security Scanners
The built-in Adobe tool covers surface-level threats. For deep server-side protection, consider these alternatives:
| Scanner | Type | What It Detects | Cost |
|---|---|---|---|
| Sansec eComscan | Server-side | File malware, DB skimmers, modified core files, rogue cron jobs | Free tier + paid plans |
| MageReport | External | Known vulnerabilities, missing patches, admin exposure | Free |
| Invicti | Enterprise DAST | XSS, SQL injection, CSRF, server misconfigurations | Enterprise pricing |
| Sucuri SiteCheck | External | Malware, blacklist status, outdated software | Free scan, paid cleanup |
Sansec eComscan deserves attention. Sansec maintains the malware signature database that powers Adobe's own Security Scan Tool. Their standalone eComscan product goes further: it scans your server file system, database tables, running processes, and scheduled tasks. It supports Magento, WooCommerce, and Shopware.
MageReport (by Hypernode) provides a quick free external scan. Enter your store URL and get results on common vulnerabilities in seconds. Use it between scheduled scans for ad-hoc checks after deployments.
Recommended approach: Use Adobe's tool for scheduled monitoring, run a server-side scanner like eComscan once a month, and use MageReport for quick checks after code changes.
Magento Security Best Practices Beyond Scanning
Scanning catches problems after they appear. These practices prevent them.
Enable Two-Factor Authentication (2FA)
Adobe Commerce includes built-in 2FA for admin accounts. Every admin user should have it active. This single measure blocks most brute-force and credential-stuffing attacks. Pair 2FA with strong passwords and limited admin accounts.
Deploy a Web Application Firewall (WAF)
A web application firewall blocks malicious traffic before it reaches your store. WAFs filter SQL injection attempts, XSS attacks, and known exploit patterns at the network edge. Cloud-based WAFs add protection without server overhead.
Apply Security Patches Fast
Adobe releases security patches for Commerce multiple times per year, with isolated fixes as needed between major patch cycles. The March 2026 bulletin (APSB26-05) addressed 21 CVEs, including 6 critical vulnerabilities. Attackers reverse-engineer patches within days of release. Real attacks prove the urgency: CosmicSting (CVE-2024-34102) compromised 5% of all Magento stores in 2024, and SessionReaper (CVE-2025-54236) targeted 81% of stores in late 2025. Test in staging first, then deploy to production fast. Our guide covers how to install Magento 2 security patches in detail.
Implement Content Security Policy (CSP)
CSP headers restrict what resources your storefront can load. This blocks cross-site scripting attacks and unauthorized script injection. Start with CSP in report-only mode, then enforce it once you verify no legitimate resources are blocked.
Configure reCAPTCHA
Protect login forms, registration pages, and checkout from automated bots. Adobe Commerce supports reCAPTCHA v2 and v3 out of the box. Configure it for both admin and storefront forms to stop automated submissions.
Choose Secure Hosting Infrastructure
Your hosting environment forms the foundation of store security. A hosting provider that handles server hardening, automated backups, DDoS protection, and infrastructure-level firewalls removes the burden of server security from your team.
Pros and Cons of the Magento Security Scan Tool
| Pros | Cons |
|---|---|
| Free for all Adobe Commerce and Open Source users | Cannot scan server file system or database |
| Runs 21,000+ tests with Sansec signatures | Detects threats after they exist, not in real time |
| Weekly or daily scheduled scans with email alerts | Limited to storefront-accessible vulnerabilities |
| Historical reports track security improvements | False positives require manual review |
| Built-in Ignore feature for false positives | No protection against zero-day exploits |
Scanning Finds Issues. Hosting Prevents Most of Them.
Security scan tools tell you what's wrong after the fact. The real question: what prevents issues from happening in the first place? Three server-level controls block most common Magento attacks: a web application firewall (WAF) that filters malicious requests before they hit PHP, automatic patch deployment within 24 hours of Adobe's releases, and file-integrity monitoring that detects tampered code.
Self-hosted teams configure these manually: ModSecurity or Cloudflare WAF, cron-based patch monitoring, and file-diff tooling. Managed Magento hosts bundle all three as core services, so a scan becomes verification instead of the primary defense. For stores without a dedicated security operations team, managed hosting with Magento-specific hardening covers WAF, automatic patching, and continuous monitoring as part of the service.
FAQ
What does the Magento Security Scan Tool cost?
The tool is free for all Adobe Commerce and Magento Open Source users. Access it through your account.magento.com dashboard. No software installation is required.
How many security tests does the tool run?
Each scan executes over 21,000 individual security tests. These cover known malware patterns, missing patches, configuration weaknesses, and vulnerability signatures maintained by Sansec.
Can the Magento Security Scan Tool detect all types of malware?
No. The tool scans from outside your server. It cannot detect malware in your file system, database, or server processes. Use a server-side scanner like Sansec eComscan for deep malware detection.
How often should I run security scans?
Run scheduled scans at least once per week. Add on-demand scans after every extension installation, Magento version upgrade, custom code deployment, or suspected security incident.
Does the tool work with PWA storefronts?
Yes. Adobe supports PWA storefronts. The verification process differs: add the confirmation META tag to packages/venia-concept/template.html, build, and deploy via Git instead of using the Admin panel.
What should I do when a scan reports failed checks?
Review each failed check and its recommended action. Prioritize critical and high-severity issues. Apply patches, update configurations, or remove vulnerable extensions as directed. Engage your development team for complex vulnerabilities.
How do I handle false positives?
Use the built-in Ignore feature to mark known false positives. This excludes them from your risk score. Common cases include patches applied through alternative methods and intentional configuration choices. Restore ignored items at any time.
Is the Security Scan Tool enough for PCI compliance?
No. The tool is one layer of a security strategy, not a PCI compliance solution. PCI DSS requires server-level controls, network segmentation, access management, and penetration testing beyond what this tool provides.
What is the latest Magento security patch?
As of March 2026, the latest security update is APSB26-05 with 21 CVEs including 6 critical vulnerabilities. Patched versions: Adobe Commerce 2.4.8-p4, 2.4.7-p9, and 2.4.6-p14.
Can I scan staging and development environments?
Yes. Configure separate scans for each domain, including staging and development URLs. Each domain requires its own verification. This approach catches vulnerabilities before they reach production.
Conclusion
The Magento Security Scan Tool provides a solid baseline for store security monitoring. Its 21,000+ tests and Sansec-powered malware signatures catch the most common threats at zero cost.
External scanning alone is not enough. Combine it with server-side scanners, regular patch updates, 2FA, WAF protection, and a secure hosting foundation.
Your server environment matters as much as your application code. Managed Magento hosting providers handle server hardening, automated patching, and infrastructure monitoring so your team can focus on growing the business instead of fighting security threats.
